Construction was among the top five business sectors targeted by cyberattacks in the second quarter of 2018, according to the latest “threat report” released earlier this month by eSentire, the largest pure-play managed detection and response service provider.
Based on intelligence gathered from more than 2,000 proprietary network and host-based detection sensors distributed globally in multiple industries, eSentire estimates that the number of attacks on Microsoft Internet Information Services (IIS) jumped to 1.7 million in the second quarter, from 2,000 in the first quarter. Most sources targeting IIS web servers originated from China-based IP addresses: according to Shodan, the global search engine for Internet-connected devices, there are 3.5 million IIS web servers exposed (with 1 million in China). The compromised servers largely originated from the Tencent and Alibaba sites.
eSentire observed IIS and WebLogic attacks originating from servers hosting Apache, RDP, SQL, IIS, and HTTP API services. Most of the records included known potential vulnerabilities based on server software version. Vulnerability records for attacking servers showed a steady increase. The majority of this growth appeared to come from Apache HTTP Servers, version 2.4.23. In the same period, records reporting vulnerabilities in IIS 7.5 and HTTP Server 2.4.10 appeared to diminish.
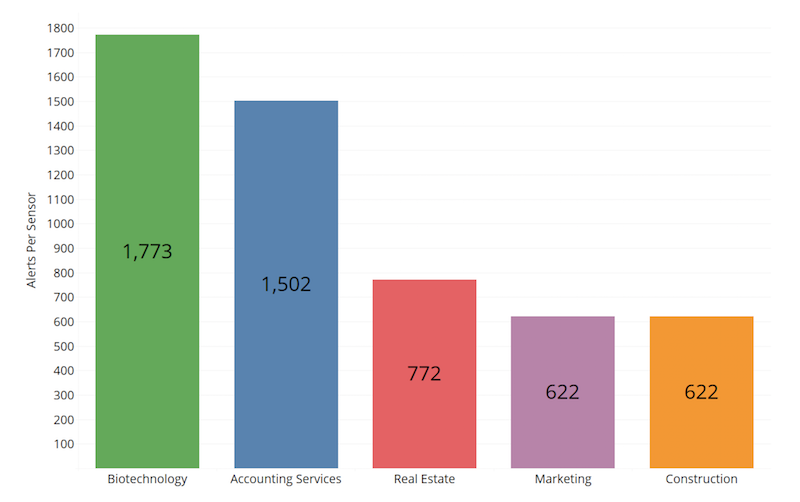
Four million potentially hostile events resulted in 57,000 alerts having been sent from eSentire’s SOC (Security Operations Center) between April 1 and June 30, 2018. Normalizing by sensor count, the top five affected industries were Biotechnology, Accounting Services, Real Estate, Marketing, and Construction. Regardless of industry, most attackers are probably looking to drive ad revenue or adopt compromised servers into their attack infrastructure, the report suggests.
The reason attacks continue, posits the report, is because most organizations have internal systems they hesitate to update for fear it will change or break something. These systems are sometimes accidentally exposed to background internet radiation which includes a firehose of exploits. Or, they are unaware that a patch is necessary or underestimate the gravity of failing to patch. This is an easily rectifiable problem that nevertheless lingers for many businesses.
There also was an increase, in general, in phishing attacks that used shipping invoice lures, despite an overall decline in the use of DocuSign—which facilities the exchanges of contracts and signed documents—as lures. Construction, Education, and Marketing experienced the largest amount of confirmed phishing attacks, with DocuSign dominating the lures observed; likely, these industries make frequent use of DocuSign in handling digital invoices and quotes due to remotely based business relationships and employees.
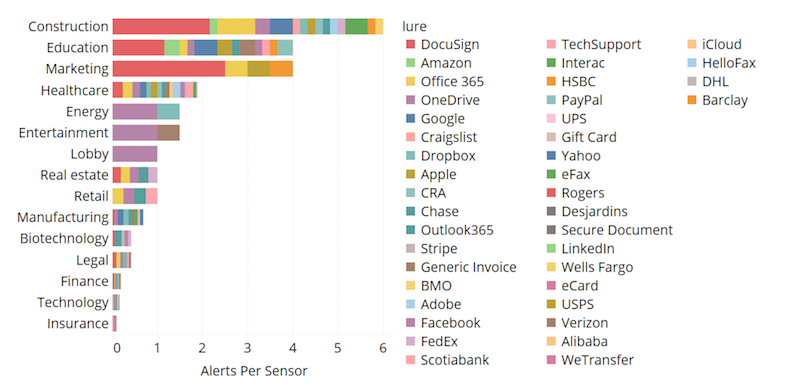
Construction was vulnerable to phishing attacks that used DocuSign as their primary lure. Image: eSentire
Real Estate experienced high volumes of D-Link home router exploit attempts. Marketing was subjected to a high volume of D-Link exploit attempts and a sizable degree of malicious PowerShell activity. And Construction experienced a large amount of Drupalgeddon2 attacks (the name given to an extremely critical vulnerability Drupal maintainers patched in late March).
PowerShell is a task-based command-line shell and scripting language built on .NET. PowerShell helps system administrators, and power-users can rapidly automate tasks that manage operating systems (Linux, macOS, and Windows) and processes. PowerShell commands let you manage computers from the command line.
In Q2 2018, the eSentire detection surface revealed that an obfuscated PowerShell realized an increase of 50% in commands, partly due to Emotet, a sophisticated malware.
Emotet, a four-year-old banking trojan, continues to evolve and emerge; antivirus solutions detected it, on average, only 22% of the time in the quarter. Emotet remains a popular choice for threat actors and was the most frequently observed malware due to numerous version updates and feature additions since it was first reported in 2014. Obfuscated malicious PowerShell commands increased 50% in Q2 2018.
Nearly half (49%) of Emotet samples included “invoice,” “payment,” or “account” in their file names. For Emotet’s competitor, Hancitor, fax documents were a popular lure (25%).
To protect against Emotet and to mitigate worming capabilities, Server Message Block Protocol (SMB) communications between systems in a network should be restricted via group policy settings or in the configuration of host-based Intrusion Prevention Systems (HIPS).
Malware, which is intended to damage or disable computers and systems, breaks down into four threat levels: malicious, suspicious, benign, and ambiguous (like false positives). Construction ranked fourth—behind Healthcare, Real Estate, and Marketing—for malware events (20 per sensor), and ranked second (after Accounting Services) for reputational blocks (about 5.25 alerts per sensor), which occur when known bad Internet Protocols (IPs) are detected trying to establish connections with monitored clients. Accounting Services and Construction are known to have large threat surfaces.
Some IPs only attempted an IIS or WebLogic exploit, while other IPs attempted both. The IPs attempting IIS and WebLogic persisted throughout the quarter, said eSentire, but those tended to rise with the emergence of other potential campaigns, indicating some threat actors may have an array of botnets in different configurations.
Related Stories
| Aug 11, 2010
Let There Be Daylight
The new public library in Champaign, Ill., is drawing 2,100 patrons a day, up from 1,600 in 2007. The 122,600-sf facility, which opened in January 2008, certainly benefits from amenities that the old 40,000-sf library didn't have—electronic check-in and check-out, new computers, an onsite coffeehouse.
| Aug 11, 2010
BIM school, green school: California's newest high-performance school
Nestled deep in the Napa Valley, the city of American Canyon is one of a number of new communities in Northern California that have experienced tremendous growth in the last five years. Located 42 miles northeast of San Francisco, American Canyon had a population of just over 9,000 in 2000; by 2008, that figure stood at 15,276, with 28% of the population under age 18.
| Aug 11, 2010
Platinum Award: The Handmade Building
When Milwaukee's City Hall was completed in 1896, it was, at 394 feet in height, the third-tallest structure in the United States. Designed by Henry C. Koch, it was a statement of civic pride and a monument to Milwaukee's German heritage. It was placed on the National Register of Historic Places in 1973 and designated a National Historic Landmark in 2005.
| Aug 11, 2010
Great Solutions: Products
14. Mod Pod A Nod to Flex Biz Designed by the British firm Tate + Hindle, the OfficePOD is a flexible office space that can be installed, well, just about anywhere, indoors or out. The self-contained modular units measure about seven feet square and are designed to serve as dedicated space for employees who work from home or other remote locations.
| Aug 11, 2010
Special Recognition: Kingswood School Bloomfield Hills, Mich.
Kingswood School is perhaps the best example of Eliel Saarinen's work in North America. Designed in 1930 by the Finnish-born architect, the building was inspired by Frank Lloyd Wright's Prairie Style, with wide overhanging hipped roofs, long horizontal bands of windows, decorative leaded glass doors, and asymmetrical massing of elements.
| Aug 11, 2010
The pride of Pasadena
As a shining symbol of civic pride in Los Angeles County, Pasadena City Hall stood as the stately centerpiece of Pasadena's Civic Center since 1927. To the casual observer, the rectangular edifice, designed by San Francisco Classicists John Bakewell, Jr., and Arthur Brown, Jr., appeared to be aging gracefully.
| Aug 11, 2010
Great Solutions: Technology
19. Hybrid Geothermal Technology The team at Stantec saved $800,000 in construction costs by embedding geothermal piping into the structural piles at the WestJet office complex in Calgary, Alb., rather than drilling boreholes adjacent to the building site, which is the standard approach. Regular geothermal installation would have required about 200 boreholes, each about four-inches in diameter ...