Construction was among the top five business sectors targeted by cyberattacks in the second quarter of 2018, according to the latest “threat report” released earlier this month by eSentire, the largest pure-play managed detection and response service provider.
Based on intelligence gathered from more than 2,000 proprietary network and host-based detection sensors distributed globally in multiple industries, eSentire estimates that the number of attacks on Microsoft Internet Information Services (IIS) jumped to 1.7 million in the second quarter, from 2,000 in the first quarter. Most sources targeting IIS web servers originated from China-based IP addresses: according to Shodan, the global search engine for Internet-connected devices, there are 3.5 million IIS web servers exposed (with 1 million in China). The compromised servers largely originated from the Tencent and Alibaba sites.
eSentire observed IIS and WebLogic attacks originating from servers hosting Apache, RDP, SQL, IIS, and HTTP API services. Most of the records included known potential vulnerabilities based on server software version. Vulnerability records for attacking servers showed a steady increase. The majority of this growth appeared to come from Apache HTTP Servers, version 2.4.23. In the same period, records reporting vulnerabilities in IIS 7.5 and HTTP Server 2.4.10 appeared to diminish.
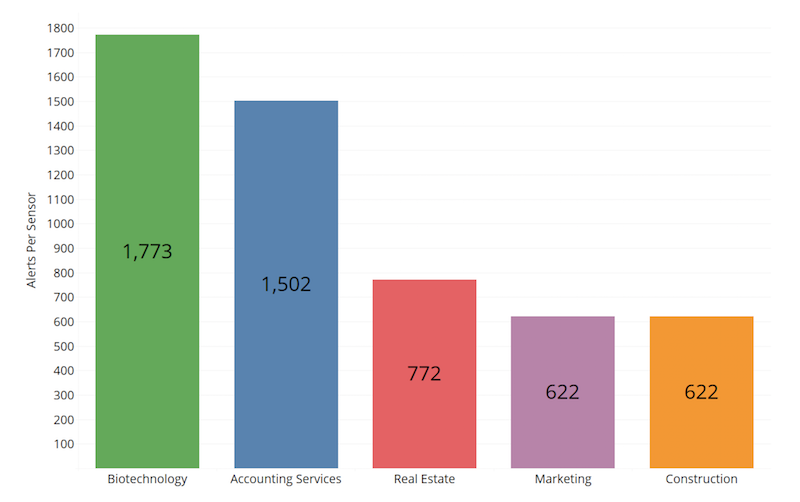
Four million potentially hostile events resulted in 57,000 alerts having been sent from eSentire’s SOC (Security Operations Center) between April 1 and June 30, 2018. Normalizing by sensor count, the top five affected industries were Biotechnology, Accounting Services, Real Estate, Marketing, and Construction. Regardless of industry, most attackers are probably looking to drive ad revenue or adopt compromised servers into their attack infrastructure, the report suggests.
The reason attacks continue, posits the report, is because most organizations have internal systems they hesitate to update for fear it will change or break something. These systems are sometimes accidentally exposed to background internet radiation which includes a firehose of exploits. Or, they are unaware that a patch is necessary or underestimate the gravity of failing to patch. This is an easily rectifiable problem that nevertheless lingers for many businesses.
There also was an increase, in general, in phishing attacks that used shipping invoice lures, despite an overall decline in the use of DocuSign—which facilities the exchanges of contracts and signed documents—as lures. Construction, Education, and Marketing experienced the largest amount of confirmed phishing attacks, with DocuSign dominating the lures observed; likely, these industries make frequent use of DocuSign in handling digital invoices and quotes due to remotely based business relationships and employees.
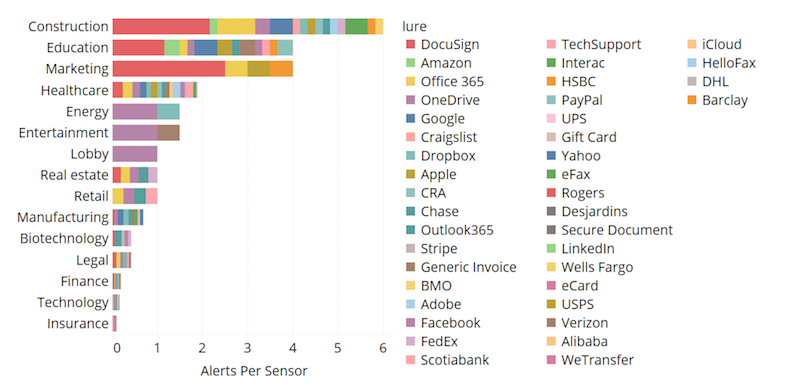
Construction was vulnerable to phishing attacks that used DocuSign as their primary lure. Image: eSentire
Real Estate experienced high volumes of D-Link home router exploit attempts. Marketing was subjected to a high volume of D-Link exploit attempts and a sizable degree of malicious PowerShell activity. And Construction experienced a large amount of Drupalgeddon2 attacks (the name given to an extremely critical vulnerability Drupal maintainers patched in late March).
PowerShell is a task-based command-line shell and scripting language built on .NET. PowerShell helps system administrators, and power-users can rapidly automate tasks that manage operating systems (Linux, macOS, and Windows) and processes. PowerShell commands let you manage computers from the command line.
In Q2 2018, the eSentire detection surface revealed that an obfuscated PowerShell realized an increase of 50% in commands, partly due to Emotet, a sophisticated malware.
Emotet, a four-year-old banking trojan, continues to evolve and emerge; antivirus solutions detected it, on average, only 22% of the time in the quarter. Emotet remains a popular choice for threat actors and was the most frequently observed malware due to numerous version updates and feature additions since it was first reported in 2014. Obfuscated malicious PowerShell commands increased 50% in Q2 2018.
Nearly half (49%) of Emotet samples included “invoice,” “payment,” or “account” in their file names. For Emotet’s competitor, Hancitor, fax documents were a popular lure (25%).
To protect against Emotet and to mitigate worming capabilities, Server Message Block Protocol (SMB) communications between systems in a network should be restricted via group policy settings or in the configuration of host-based Intrusion Prevention Systems (HIPS).
Malware, which is intended to damage or disable computers and systems, breaks down into four threat levels: malicious, suspicious, benign, and ambiguous (like false positives). Construction ranked fourth—behind Healthcare, Real Estate, and Marketing—for malware events (20 per sensor), and ranked second (after Accounting Services) for reputational blocks (about 5.25 alerts per sensor), which occur when known bad Internet Protocols (IPs) are detected trying to establish connections with monitored clients. Accounting Services and Construction are known to have large threat surfaces.
Some IPs only attempted an IIS or WebLogic exploit, while other IPs attempted both. The IPs attempting IIS and WebLogic persisted throughout the quarter, said eSentire, but those tended to rise with the emergence of other potential campaigns, indicating some threat actors may have an array of botnets in different configurations.
Related Stories
| Nov 11, 2013
The story behind 'Pedia-Pod,' BD+C's modular pediatric patient unit at Greenbuild
In the November issue of BD+C, you'll see our report on "Pedia-Pod," the modular pediatric patient unit we've helped design, outfit, and build at Greenbuild. Here's how it was developed.
| Nov 8, 2013
Can Big Data help building owners slash op-ex budgets?
Real estate services giant Jones Lang LaSalle set out to answer these questions when it partnered with Pacific Controls to develop IntelliCommand, a 24/7 real-time remote monitoring and control service for its commercial real estate owner clients.
| Nov 8, 2013
S+T buildings embrace 'no excuses' approach to green labs
Some science-design experts once believed high levels of sustainability would be possible only for low-intensity labs in temperate zones. But recent projects prove otherwise.
| Nov 8, 2013
Walkable solar pavement debuts at George Washington University
George Washington University worked with supplier Onyx Solar to design and install 100 sf of walkable solar pavement at its Virginia Science and Technology Campus in Ashburn, Va.
| Nov 6, 2013
Energy-efficiency measures paying off for commercial building owners, says BOMA study
The commercial real estate industry’s ongoing focus on energy efficiency has resulted in a downward trend in total operating expenses (3.9 percent drop, on average), according to BOMA's Experience Exchange Report.
| Nov 5, 2013
Net-zero movement gaining traction in U.S. schools market
As more net-zero energy schools come online, school officials are asking: Is NZE a more logical approach for school districts than holistic green buildings?
| Oct 31, 2013
74 years later, Frank Lloyd Wright structure built at Florida Southern College
The Lakeland, Fla., college adds to its collection of FLW buildings with the completion of the Usonian house, designed by the famed architect in 1939, but never built—until now.
| Oct 30, 2013
15 stellar historic preservation, adaptive reuse, and renovation projects
The winners of the 2013 Reconstruction Awards showcase the best work of distinguished Building Teams, encompassing historic preservation, adaptive reuse, and renovations and additions.
| Oct 30, 2013
11 hot BIM/VDC topics for 2013
If you like to geek out on building information modeling and virtual design and construction, you should enjoy this overview of the top BIM/VDC topics.
| Oct 20, 2013
What you missed at BUILDINGChicago/Greening the Heartland
Not able to attend the inaugural BUILDINGChicago/Greening the Heartland conference and expo this week? Don't worry. The BD+C editorial team has you covered.